[ MITRE ATT&CK Stacks ]
Advanced threat simulation
Stacks in this section give you an effective way to practice MITRE ATT&CK TTPs through a high degree emulation of the target infrastructure. You get the real experience of an adversary. The scenarios are based on MITRE & ATTACK matrix.
Learn more about stacks
18 Exfiltration - 02
Beginner
- Protocol Impersonation
- Stealth Exfiltration
- Stealth Exfiltration
17 Discovery - Linux
Beginner
- Process Discovery
- Threat Detection
- Integrity Verification
16 File Analysis - Linux
Beginner
- File Analysis
- Threat Detection
- Integrity Verification
15 Defense Evasion - Network
Intermediate
- Port Manipulation
- Session Splicing
- Payload Obfuscation
- Route Manipulation
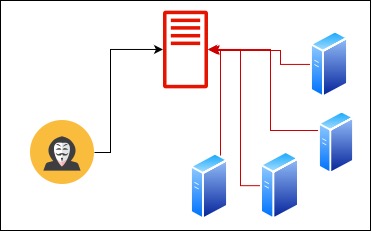
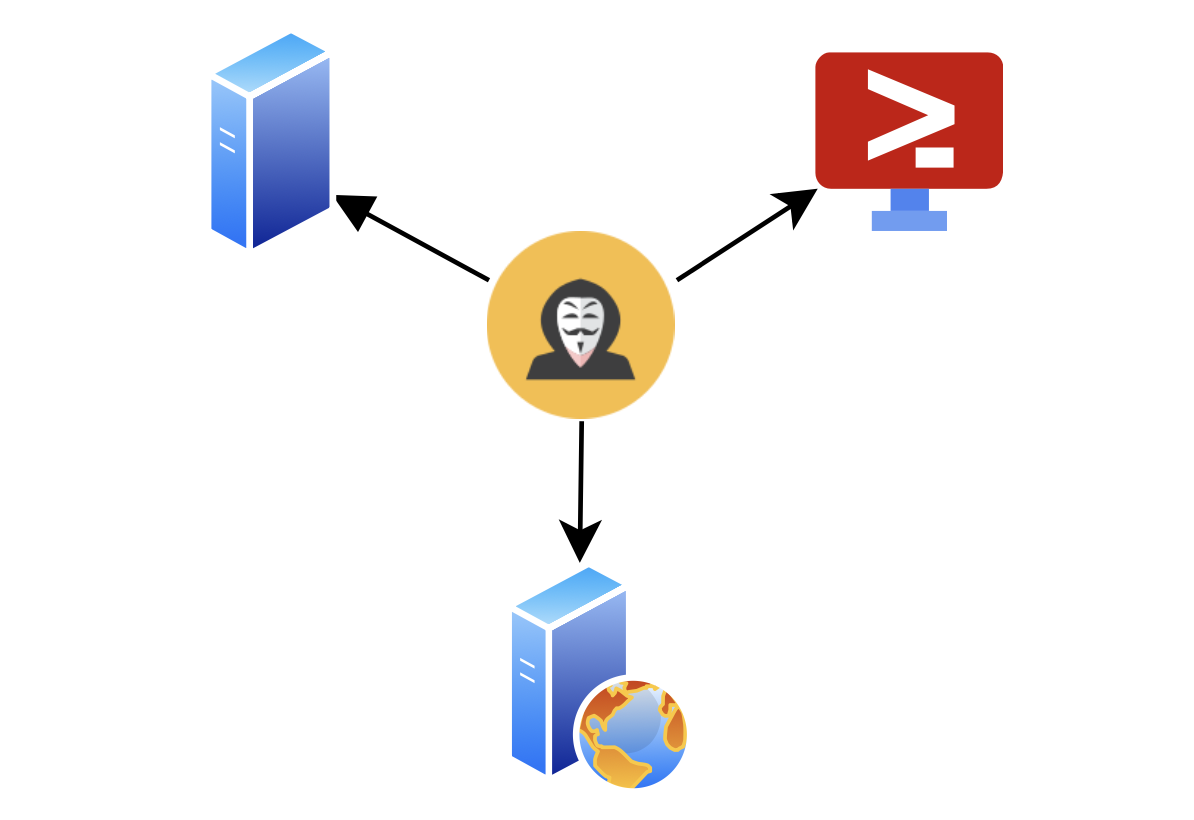
14 Command & Control - Armitage
Beginner
- C2 Environment
- Create and Manage Listeners
- Perform Host Enumeration
13 Credential Access - Password Cracking
Beginner
- Understand Hashes
- Apply Unshadowing
- Simulate an Attacker’s Approach
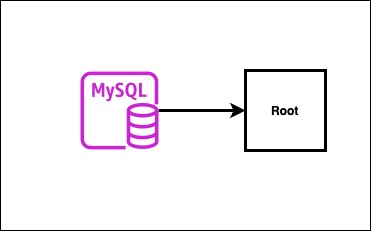
12 Privilege Escalation - MySQL
Intermediate
- Understand MySQL Vulnerabilities
- Exploit Vulnerabilities with Metasploit
- Simulate an Attacker’s Approach

11 Initial Access - Wordpress
Beginner
- Understand WordPress Vulnerabilities
- Exploit Vulnerabilities with Metasploit
- Simulate an Attacker’s Approach
10 Persistence - Linux
Beginner
- Understand Persistence Mechanisms
- Identify and Mitigate Unauthorized Access
- Inject SSH Keys
09 Execution - x86_64 Assembly
Beginner
- Explore stack manipulation
- Practice conditional branching
08 Execution - buffer overflow
Beginner
- Enumeration and execution
- Gain hands-on experience with industry-standard cybersecurity tools
02 Reconnaissance - Passive
Beginner
- Enumeration and reconnaissance
- Gain hands-on experience with industry-standard cybersecurity tools
07 Resource Development - 1
Intermediate
- Pentesting strategies and tactics
- Enumeration and reconnaissance
- Gain hands-on experience with industry-standard cybersecurity tools

05 Reconnaissance - Target
Intermediate
- Pentesting strategies and tactics
- Enumeration and reconnaissance
- Gain hands-on experience with industry-standard cybersecurity tools
04 Reconnaissance - OSINT
Beginner
- Enumeration and reconnaissance
- Gain hands-on experience with industry-standard cybersecurity tools
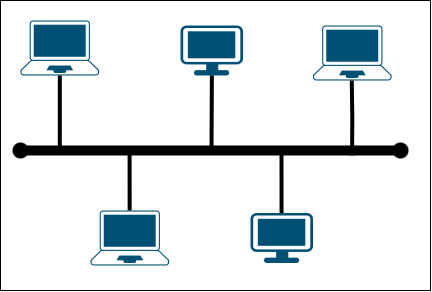
01 Networking 101
Beginner
- Network Fundamentals
- Reconnaissance
03 Reconnaissance - Network
Beginner
- Pentesting strategies and tactics
- Enumeration and reconnaissance